Protecting Remote Workforce Beyond the Perimeter
According to a recent survey from the Pew Research Center, 71% of the workforce are working remotely today, compared to 20% before the pandemic. Since the SolarWinds Attack on December 2020, the security landscape has dramatically changed.
Employees working from home are not equipped to stop cyberattacks. Cyber-criminals are taking advantage of the lack of security controls in home routers, personal computers and BYOD devices, to steal corporate credentials and sensitive information. Weaknesses and misconfigurations in corporate laptops, in addition to the stress some people are experiencing due to the new working conditions and from the pandemic itself, do not help the situation.

Remote workforce deserves a comprehensive solution that reduces the attack surface by stopping ransomware, phishing and drive-by attacks.
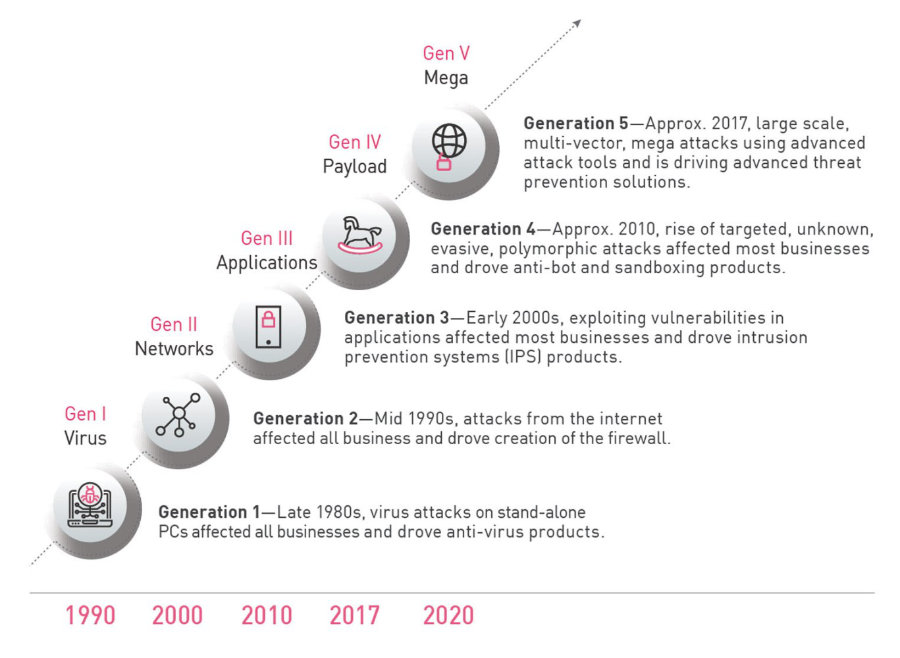
Being in the cyber security space for many years, I noticed cyber-attacks are more sophisticated and difficult to detect, and there is no indication of slowing down. Cyber-criminals target people, as they are the weakest point in the company. They use deception techniques to play with people’s minds to make them go to malicious websites to steal corporate user names and passwords or to make them download malicious files and implant malicious code in trusted environments that later will be activated as ransomware to take the data hostage for ransom. To add more heat to the fire, as more people are working remotely, home routers provided by Internet Service Providers (ISP) are not equipped to stop Fifth Generation of cyber-attacks.
Remote workers access applications hosted in the cloud or in the datacenter from anywhere using their laptops or mobile devices. The process of securing access of these applications from anywhere involves many vendors, which causes basically three problems:
- First, It creates security gaps due to the lack of visibility.
- Second, It is very complex due to the number of management consoles required to access and support the solution.
- Third, The lack of integration that provides full visibility in a consolidated management security console.
On the other hand, users are the weakest point on the network, and despite the efforts companies do to inject security awareness into the organizational culture, users tend to forget what they have learned as weeks go by and come back to the old habits.
Therefore, users are just one click away to allow malware to enter the organization. Cyber-psychology tells us that users tend to trust more the sender of the message than the actual message. If users trust the sender, they will lower their shields and will consider the message genuine. If the message comes from hacker pretending to be the CEO, CFO, or anybody with authority in the company, users will do what the message says.
After the SolarWinds attack, the security landscape has changed. Several organizations were compromised. Malicious code was injected in trusted environments and only time will tell when it will be activated. Ransomware attacks continue to surge globally, hitting a 93% increase year on year.
Remote workforce need a different cyber security strategy to protect themselves from the increased cyber-attacks.
To lower the attack surface on remote users, organizations should consider looking at modern endpoint solution that closes the security gap by encapsulating security controls under a single management console to prevent most of the imminent attacks such as phishing, drive-by malware and ransomware.
The endpoint solution should be part of a security ecosystem assisted by real-time threat intelligence feeds, sandboxing, machine learning, AI-behavioral algorithms, file restoration, and deep forensics analysis that goes beyond traditional detection methods for a higher catch rate.
Fortunately, there is a solution to protect the remote workforce working from anywhere, outside the company’s security perimeter. Check Point Harmony Endpoint prevents and stops unknown and zero-day attacks with Next Generation AV, Anti-Malware, Anti-phishing, Sandboxing and Content Disarming Reconstruction technologies. It has a runtime protection in place to address and remediate those attacks with Behavioral Analysis, Anti-Ransomware, Anti-Exploit.
Check out the demo video from Check Point’s security architect Aaron Rose demonstrating the efficiency of Check Point’s Anti-Ransomware against several ransomware attacks.
I firmly believe Check Point Harmony Endpoint meets the new strategy remote workforce needs with the assurance to access applications from anywhere safely. Harmony Endpoint closes the security gaps and reduce the attack surface with its Anti-Ransomware technology keeping the remote workforce safe.
The security landscape has changed dramatically since the SolarWinds Attack. Cyber-criminals implanted malicious code in trusted environments that could potentially be activated as Ransomware at any time. No one really knows when the next attack will happen but you must be ready for the next attack.
Harmony Endpoint is the complete endpoint security solution to navigate today’s threat landscape. It prevents more threats before they reach the device with a focus on sophisticated attacks. It cleans the entire kill chain and automates most of the analyst work so the SOC teams can focus on the tasks that really matter.
Are you ready to take control of your endpoint security and bring the harmony your remote workforce needs?
Take the 90-day free evaluation of Check Point Harmony, full stack including Anti-Ransomware.
- Miguel Angulo
- Blogs